Performance analysis of Wireless Sensor Networks (WSNs) is considered as an important and interesting process. Numerous simulators are useful for carrying out this process in an effective way. To conduct this, we provide essential guidelines in a step-by-step manner:
Performance Assessment of Wireless Sensor Networks (WSNs) with Simulators
For various major applications such as industrial automation, healthcare, and ecological tracking, Wireless sensor Networks (WSNs) are most significant. To assure scalability, effectiveness, and credibility, analyzing the performance of WSNs is very important. For assessing the WSNs performance based on different constraints, various simulators offer efficient environments. Some of the major simulators are TOSSIM, OMNeT++, and Ns-3.
In order to carry out performance assessment of WSN with NS-3, consider the following detailed instruction:
Procedural Instruction with NS-3
Step 1: Install NS-3
- Download NS-3
- Download the current version of NS-3 by accessing its official website.
- Install Dependencies:
sudo apt-get update
sudo apt-get install gcc g++ python3 cmake libc6-dev libc6-dev-i386 libclang-dev automake autoconf mercurial
- Extract and Build NS-3:
tar xjf ns-allinone-3.xx.tar.bz2
cd ns-allinone-3.xx
./build.py –enable-examples –enable-tests
Step 2: Develop a New Simulation Script
- Direct to the scratch File:
cd ns-allinone-3.xx/ns-3.xx/scratch
- Develop a New Script File:
touch wsn-simulation.cc
touch wsn-simulation.cc
Step 3: Draft the Simulation Script
As a means to simulate a WSN including performance assessment, examine the below specified fundamental sample script:
#include “ns3/core-module.h”
#include “ns3/network-module.h”
#include “ns3/internet-module.h”
#include “ns3/applications-module.h”
#include “ns3/mobility-module.h”
#include “ns3/energy-module.h”
#include “ns3/lr-wpan-module.h”
#include “ns3/sixlowpan-module.h”
using namespace ns3;
NS_LOG_COMPONENT_DEFINE (“WSNPerformanceAnalysis”);
void PacketReceivedCallback(Ptr<const Packet> packet, const Address &address) {
NS_LOG_UNCOND(“Packet received at ” << Simulator::Now().GetSeconds() << ” seconds”);
}
int main (int argc, char *argv[])
{
CommandLine cmd;
cmd.Parse (argc, argv);
// Create nodes
NodeContainer nodes;
nodes.Create (10);
// Set up Lr-WPAN devices
LrWpanHelper lrWpanHelper;
NetDeviceContainer lrwpanDevices = lrWpanHelper.Install (nodes); lrWpanHelper.AssociateToPan (lrwpanDevices, 0);
// Set up Mobility model
MobilityHelper mobility; mobility.SetPositionAllocator (“ns3::GridPositionAllocator”,
“MinX”, DoubleValue (0.0),
“MinY”, DoubleValue (0.0),
“DeltaX”, DoubleValue (10.0),
“DeltaY”, DoubleValue (10.0), “GridWidth”, UintegerValue (3), “LayoutType”, StringValue (“RowFirst”));
mobility.SetMobilityModel (“ns3::ConstantPositionMobilityModel”);
mobility.Install (nodes);
// Install Internet stack
InternetStackHelper internet;
internet.Install (nodes);
// Set up 6LoWPAN
SixLowPanHelper sixlowpan;
NetDeviceContainer sixlowpanDevices = sixlowpan.Install (lrwpanDevices);
// Assign IP addresses
Ipv6AddressHelper ipv6;
ipv6.SetBase (Ipv6Address (“2001:db8::”), Ipv6Prefix (64));
Ipv6InterfaceContainer interfaces = ipv6.Assign (sixlowpanDevices);
// Install applications
uint16_t port = 9; // Discard port
UdpEchoServerHelper server (port);
ApplicationContainer apps = server.Install (nodes.Get (1));
apps.Start (Seconds (1.0));
apps.Stop (Seconds (10.0));
UdpEchoClientHelper client (interfaces.GetAddress (1, 1), port);
client.SetAttribute (“MaxPackets”, UintegerValue (10));
client.SetAttribute (“Interval”, TimeValue (Seconds (1.0)));
client.SetAttribute (“PacketSize”, UintegerValue (1024));
apps = client.Install (nodes.Get (0));
apps.Start (Seconds (2.0));
apps.Stop (Seconds (10.0));
// Set up tracing for performance analysis
lrwpanDevices.Get (1)->TraceConnectWithoutContext (“MacRx”, MakeCallback (&PacketReceivedCallback));
// Run the simulation
Simulator::Run ();
Simulator::Destroy ();
return 0;
}
Step 4: Set up and Execute the Simulation
- Compile the Simulation Script:
cd ns-allinone-3.xx/ns-3.xx
./waf configure
./waf build
./waf –run scratch/wsn-simulation
- Examine the Result:
- Check the terminal which displays the simulation outcomes. It is approachable to analyze various major metrics like energy utilization, latency, and packet delivery ratio.
Performance Metrics to Examine
- Packet Delivery Ratio (PDR):
- By considering the efficiently delivered packets and total transmitted packets, assess the ratio.
- PDR = (Received Packets / Sent Packets) * 100
- End-to-End Delay:
- For a packet, evaluate the average time that is obtained to traverse from the source to the targeted location.
- Average Delay = Sum of Delays / Number of Received Packets
- Energy Consumption:
- At the time of simulation, the total amount of energy utilized by the nodes has to be assessed.
- To track energy utilization, the energy module in NS-3 can be employed.
- Throughput:
- For throughput, the amount of successful delivery of data through a communication channel must be evaluated.
- Throughput = (Total Received Bytes * 8) / Simulation Time.
- Latency:
- For each packet, evaluate the time that is acquired to travel the network from source to the targeted location.
- Network Lifetime:
- As far as the initial node in the network drains its energy, assess the time.
What computer networking related projects can a student in the final year of BS computer science do as minor projects?
Computer networking is an intriguing domain that facilitates data sharing and interaction among various computers by linking them. Appropriate for a final year BS Computer Science scholar, we suggest a few compelling basic project plans relevant to computer networking:
- Network Topology Design and Simulation
- Explanation: Utilize various tools such as GNS3 or Cisco Packet Tracer for modeling diverse network topologies like hybrid, mesh, ring, and star. Examine the major performance metrics such as packet loss, throughput, and latency after the simulation of network traffic.
- Basic Router and Switch Configuration
- Explanation: To arrange fundamental security platforms, static and dynamic routing (OSPF, RIP), inter-VLAN routing, and VLANs, establish switches and routers with the aid of command-line interface (CLI).
- Network Monitoring and Analysis
- Explanation: As a means to seize and examine network traffic, employ effective network tracking tools like PRTG, Nagios, or Wireshark. Based on network performance, develop explicit reports. The possible problems have to be detected, and recommend further enhancements.
- Firewall Configuration and Testing
- Explanation: Protect a concise network by arranging and establishing a firewall (for instance: pfSense). The firewall principles must be specified and applied. In securing from general assaults and obstructing illicit access, test the efficiency of firewall.
- Virtual Private Network (VPN) Setup
- Explanation: To protect remote access to a network, set up a VPN client and server (for example: OpenVPN). Various VPN protocols (like SSL/TLS, IPSec) have to be analyzed and applied. Then, their performance should be assessed.
- Network File Sharing and Permissions
- Explanation: With the aid of protocols such as NFS or SMB (Samba), arrange a network file sharing system. The user consents must be applied and handled. Assess the performance and safety of this system.
- Quality of Service (QoS) Implementation
- Explanation: In order to focus on traffic for major applications like video conferencing and VoIP, apply QoS strategies on a network. On switches and routers, arrange QoS contexts. In network performance, their implication has to be examined.
- Wireless Network Security
- Explanation: Plan to configure a wireless network and utilize WPA2/WPA3 encryption for protecting the network. Some supplementary safety techniques like hidden SSIDs and MAC address filtering must be applied. In opposition to general hazards, evaluate the safety of the network.
- IoT Device Integration and Management
- Explanation: Within a network, combine IoT devices. Utilize various protocols such as MQTT to handle their interaction. For tracking and regulating IoT devices, create an efficient dashboard.
- Network Performance Testing with iPerf
- Explanation: Assess and examine the network performance by employing iPerf. In terms of various network arrangements and constraints, evaluate metrics like packet loss, jitter, and throughput.
- Implementation of Network Redundancy
- Explanation: Employ different protocols such as GLBP, VRRP, or HSRP for modeling and executing network redundancy. The failover abilities of the network have to be tested. On credibility and accessibility, assess its implication.
- Setting Up a DNS Server
- Explanation: With the support of BIND or other DNS software, set up a DNS server. The DNS zones and logs should be applied. Assess the credibility and performance of the server.
- Voice over IP (VoIP) Configuration
- Explanation: Utilize major software such as FreePBX or Asterisk to establish a VoIP system. SIP phones, extensions, and trunks have to be arranged. Assess the VoIP calls’ credibility and standard.
- Network Automation with Python
- Explanation: Implement Python language and libraries such as NAPALM and Netmiko for automating the network arrangement and handling missions. To automate some general missions like device setup, reporting, and tracking, create scripts.
- Network Intrusion Detection System (IDS)
- Explanation: Make use of software such as Suricata or Snort to apply an IDS. To identify general network assaults, set up effective principles. In detecting and notifying on malicious actions, assess the efficiency of the system.
- Building a Home Lab with Virtualization
- Explanation: Employ virtualization tools such as VirtualBox or VMware for the development of a home lab setting. To simulate various networking contexts, arrange virtual networks, switches, and routers.
- Configuring a Proxy Server
- Explanation: A proxy server has to be arranged and established with the help of Squid or other proxy software. Plan to apply various approaches like access control strategies, content filtering, and caching.
- Implementing Software-Defined Networking (SDN)
- Explanation: By configuring an SDN controller with ONOS or OpenDaylight, investigate SDN principles. Using the SDN controller, set up and handle network devices. The advantages of SDN have to be examined.
- Network Traffic Analysis and Visualization
- Explanation: Utilize efficient tools such as Wireshark to seize network traffic. With the help of software such as Kibana and Elasticsearch, visualize the data. Plan to detect possible problems after examining traffic patterns.
- IPv6 Network Configuration
- Explanation: In order to enable IPv6, establish a network. IPv6 addressing and routing have to be arranged. Evaluate the appropriateness to IPv4 and the performance of the network.
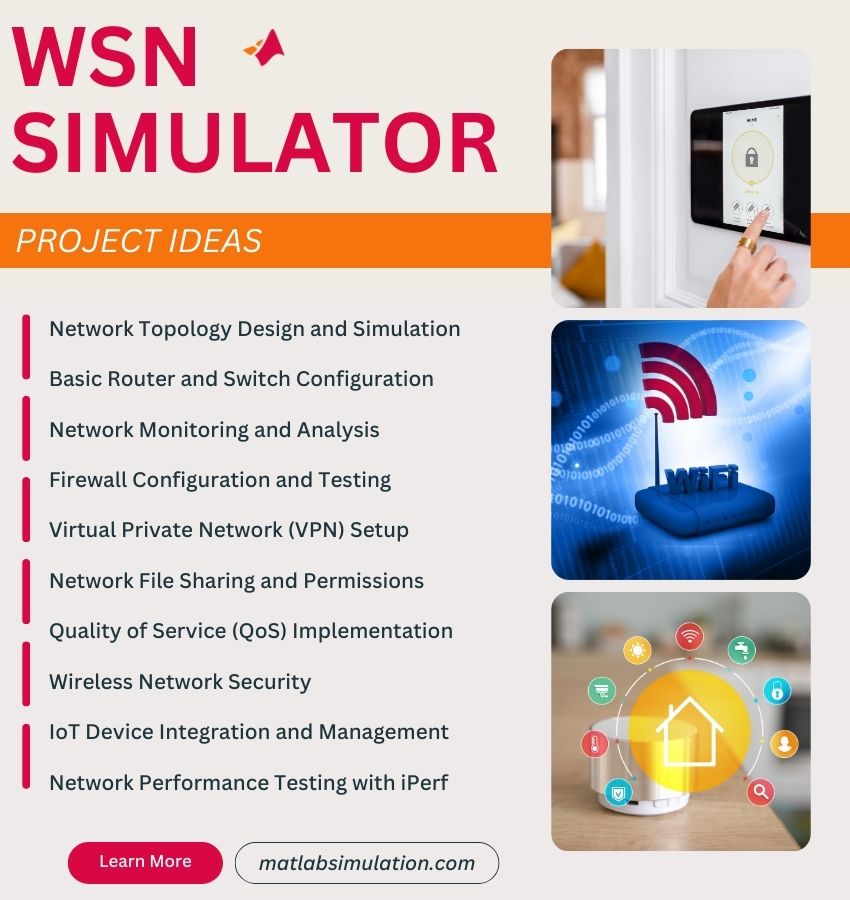
WSN Simulator Project Topics & Ideas
Here are some popular WSN Simulator Project Topics & Ideas that scholars are currently interested in. If you need personalized assistance, you can rely on matlabsimulation.com as your trusted partner. Our squad of expert writers, who are all doctorates, excel in research article writing. Feel free to discuss any doubts you have with us.
- A kind of effective data aggregating method based on compressive sensing for wireless sensor network
- Market segmentation of wireless sensor system in network commodity selection
- A multi-gateway authentication and key-agreement scheme on wireless sensor networks for IoT
- DynTunKey: a dynamic distributed group key tunneling management protocol for heterogeneous wireless sensor networks
- Fuzzy-based congestion control for wireless multimedia sensor networks
- A coverage-aware energy replenishment scheme for wireless rechargeable sensor networks
- Collaborative Image Coding and Transmission over Wireless Sensor Networks
- Optimal deployment of large-scale wireless sensor networks based on graph clustering and matrix factorization
- Efficient integration of secure and safety critical industrial wireless sensor networks
- Sleep/wake scheduling scheme for minimizing end-to-end delay in multi-hop wireless sensor networks
- A Stochastic Multiobjective Optimization Framework for Wireless Sensor Networks
- Energy consumption and lifetime analysis in clustered multi-hop wireless sensor networks using the probabilistic cluster-head selection method
- Towards improved clustering and routing protocol for wireless sensor networks
- Security in cognitive wireless sensor networks. Challenges and open problems
- Perimeter Coverage Scheduling in Wireless Sensor Networks Using Sensors with a Single Continuous Cover Range
- An energy efficient MCDS construction algorithm for wireless sensor networks
- Optimal Throughput and Energy Efficiency for Wireless Sensor Networks: Multiple Access and Multipacket Reception
- Automatic ARIMA modeling-based data aggregation scheme in wireless sensor networks
- Reliability analysis for a data flow in event-driven wireless sensor networks using a multiple sending transmission approach
- Routing metrics for cache-based reliable transport in wireless sensor networks












