GNS3 is a network simulator that is used for various processes such as designing, simulating, etc. Concentrating on recent networking advancements and limitations, we provide numerous GNS3 network simulator project ideas and topics together with major parameters for assessment purposes:
- SDN (Software Defined Networking) Implementation and Optimization
- Explanation: An SDN infrastructure has to be deployed within GNS3 in order to investigate its scalability, adaptability, and effectiveness enhancements beyond cultural network models.
- Relevant Parameters: Resource usage, network delay, throughput, and control plane reactions.
- Comparative Analysis of IPv4 vs. IPv6 Deployments
- Explanations: To simulate and contrast IPv4 and IPv6 on the basis of scalability, routing performance, and safety characteristics, aim to establish dual-stack networks in GNS3.
- Relevant Parameters: Routing table size, address allotment effectiveness, safety protocols efficacy, and packet delivery ratio.
- Network Function Virtualization (NFV) for Enterprise Networks
- Explanation: Concentrating on the virtualization of load balancers, firewalls, and WAN optimizers, it is approachable to employ GNS3 to simulate the implementation of NFV in enterprise networks.
- Relevant Parameters: Capital and operational cost mitigation, scalability, implementation flexibility, and performance overhead.
- High Availability Network Designs
- Explanation: By utilizing approaches such as VRRP, GLBP, or HSRP for fault tolerance and replication, model and simulate high accessibility networks in GNS3.
- Relevant Parameters: Resource replication, failover time, traffic distribution effectiveness, and convergence time.
- IoT Network Models with Edge Computing
- Explanation: An IoT network simulation has to be developed in GNS3 in such as a manner that integrates edge computing devices to process data nearer to the resource, thereby decreasing delay and utilization of bandwidth.
- Relevant Parameters: Network congestion volume, IoT device energy utilization, data processing delay, and edge computing resource consumption.
- Performance of Cryptographic Protocols in Network Security
- Explanation: The performance influence of deploying different cryptographic protocols like SSL/TLS, IPSec in network interactions simulated in GNS3 has to be assessed.
- Relevant Parameters: Throughput, safety violation prevention performance, CPU and memory overhead on network devices, and encryption/decryption time.
- Multi-Protocol Label Switching (MPLS) Networks
- Explanation: Concentrating on VPN deployments, QoS advantages, and congestion engineering, aim to simulate MPLS implementation in service provider networks by employing GNS3.
- Relevant Parameters: VPN isolation and scalability, label switching effectiveness, traffic engineering performance, and QoS metric enhancements.
- Cloud Connectivity Models
- Explanation: By utilizing GNS3, model and simulate different cloud connectivity systems such as SD-WAN, direct connect, VPN, and it is appreciable to examine their effectiveness and safety impacts.
- Relevant Parameters: Latency, safety level, cost-efficiency, and connection balance.
- Network Scalability Testing
- Explanation: For assessing approaches such as load balancing and clustering, utilize GNS3 to simulate network advancement settings in industrial platforms.
- Relevant Parameters: Performance degradation levels, resource usage effectiveness, and network capability before and after scalability improvements.
- Wireless Network Models and Protocols
- Explanation: To research protocols such as 802.11ax or 802.11ac, incorporating GNS3 with external tools can be supportive for simulating wireless platforms, even though it concentrates only on wired networks.
- Relevant Parameters: Coverage area, co-channel interference influences, signal strength, and throughput differences with distance.
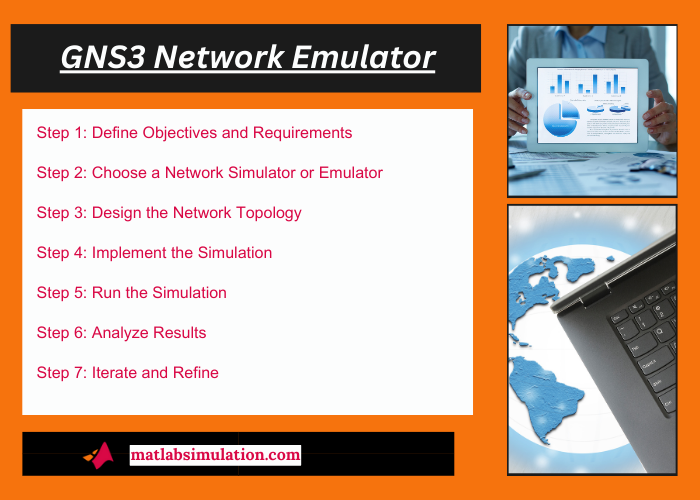
How do you create a network simulation?
The process of creating a network simulation is determined as intriguing as well as challenging. Generally, network simulations can assist in verifying network structures, interpreting activities of the network, and examining settings that might be problematic or impracticable to recreate in the actual world. The following is a stepwise instruction that help us to develop a network simulation:
Step 1: Define Goals and Necessities
- Goals: What we intend to attain with the simulation has to be described in an explicit manner. Generally, examining network protocols, investigating effectiveness under load, or interpreting the influence of variations in network topology are encompassed in the objectives.
- Necessities: It is approachable to find the necessities of our simulation such as the network protocols to be employed, the kinds of devices like switches, hosts, routers, and any certain network arrangements or settings.
Step 2: Choose a Network Simulator or Emulator
- Simulator Options: A network simulator should be selected in a way that aligns with our goals and necessities. Typically, OMNeT++, NS-3, and GNS3 are examined as the most prominent choices of simulator. Every simulator contains its own advantages, assisted protocols, and learning curve.
- Emulator vs. Simulators: It is advisable to determine whether we want an emulator which recreates network device functions more accurately or a simulator that designs the activities of the network. For instance, GNS3 has the capability to simulate as well as emulate network devices.
Step 3: Design the Network Topology
- Topology Design: Model the network topology according to our goals that we will simulate. Generally, network segments, relationships, and the design of nodes like switches, routers, end devices are encompassed.
- Device Configuration: Involving IP addressing, routing protocols, and any certain scenarios related to the objectives of our simulation, we schedule the arrangement of every device.
Step 4: Implement the Simulation
- Build the Network: We create the network by appending and linking the nodes based on our topology structure, by employing our selected simulation tool.
- Configure Devices: The scheduled arrangements have to be implemented to our devices. To establish IP addresses, routing tables, and other metrics, the process of scripting or utilizing graphical interfaces might be included.
- Traffic Generation: To simulate data transmission among nodes, it is appreciable to specify the flow of traffic within our network. The procedure of indicating the kinds of traffic like UDP, TCP, traffic levels, sources, and destinations are encompassed.
Step 5: Execute the Simulation
- Execution: By examining the activities of the network, we execute our simulation. Frequently, practices to start, pause, and stop simulations, in addition to adapting the momentum of simulation time are offered by simulators.
- Monitoring and Debugging: To track the network at the time of simulation, we utilize tools that are offered by the simulator. It is advisable to be aware of unanticipated faults or activities, and whenever required aim to modify our arrangement.
Step 6: Analyze Findings
- Data Collection: The data produced by the simulation has to be gathered. Typically, delay measurements, throughput diagrams, records, and packet flows are involved.
- Analysis: To create conclusions regarding network effectiveness, activities, and the influence of various arrangements, we examine the gathered data. Various tools can be very helpful such as custom scripts for data processing or Wireshark for packet analysis.
Step 7: Iterate and Refine
- Iteration: To investigate various settings or solve any identified problems, we make alterations to our network system or arrangement according to our exploration.
- Documentation: Normally, our simulation arrangement, execution processes, outcomes, and any conclusions created has to be reported. For repeatability and upcoming investigation purposes, this step is determined as most significant.
GNS3 Network Emulator Project Topics & Ideas
Numerous developments have been achieved in the realm of GNS3 Network Emulator. Below are some examples of Project Topics & Ideas that we have recently worked on. Feel free to share your inquiries with us to maximize the benefits of our services.
- A game theory based trust model for Vehicular Ad hoc Networks (VANETs)
- Prediction-based protocols for vehicular Ad Hoc Networks: Survey and taxonomy
- Design and performance evaluation of cross layered MAC and clustering solutions for wireless ad hoc networks
- Throughput-oriented MAC for mobile ad hoc networks: A game-theoretic approach
- Clustering overhead and convergence time analysis of the mobility-based multi-hop clustering algorithm for mobile ad hoc networks
- Capacity fades analysis of MIMO Rician channels in mobile ad hoc networks
- A Distributed Self-Adaptive Intrusion Detection System for Mobile Ad-hoc Networks Using Tamper Evident Mobile Agents
- Improved ant colony-based multi-constrained QoS energy-saving routing and throughput optimization in wireless Ad-hoc networks
- Using an evolutionary algorithm to optimize the broadcasting methods in mobile ad hoc networks
- Fault tolerant time synchronization using offsets table robust broadcasting protocol for vehicular ad hoc networks
- A Novel Reaction Scheme against the MAC Layer Misbehavior in Mobile Ad Hoc Networks
- A Hybrid Backbone Based Clustering Algorithm for Vehicular Ad-Hoc Networks
- Opportunistic topology control for ad hoc wireless network survivability enhancement based on LIMOS model
- Placement of SDN controllers based on network setup cost and latency of control packets
- A comprehensive survey on SDN and blockchain-based secure vehicular networks
- Detecting and mitigating DDoS attacks with moving target defense approach based on automated flow classification in SDN networks
- A Graph reinforcement learning based SDN routing path selection for optimizing long-term revenue
- SDN-based automated rekey of IPsec security associations: Design and practical validations
- Data plane failure and its recovery techniques in SDN: A systematic literature review
- Optimizing incremental SDN upgrades for load balancing in ISP networks












